ISO standards are standards that define the steps and measures to be followed in different fields.
They are designed to standardize a set of procedures, which affects both the way a product is manufactured and the management of materials.

The ISO 27001 standard establishes a guide with the characteristics that must be put in place to build an information security management system (ISMS) in a company.
This standard in particular is recognized as one of the most popular among all ISO international standards.
An effective information security management system
The ISO 27001 standard places people, technology and procedures at the center of its mission, to put out the best steps to follow when it comes to IT data security.
A company may consider ISO 27001 certification to improve its image by ensuring a secure and reliable environment and service for its customers.
Likewise, it gives the company additional credibility in the eyes of its staff. However, this does not mean that a company that does not have its certification is not competent.
It simply means that organizations that have their ISO 27001 certification are recognized by international standards as companies that take the necessary steps to provide a secure service.
Other benefits of becoming ISO 27001 certified:
- Reduce and control the risk of vulnerabilities in your organization’s IT environment
- Reduce long-term costs
- Reduce the risk of being attacked, hacked or victimized by phishing companies
- Be compliant with international requirements
- Allows you to raise the level of awareness of your company’s employees.
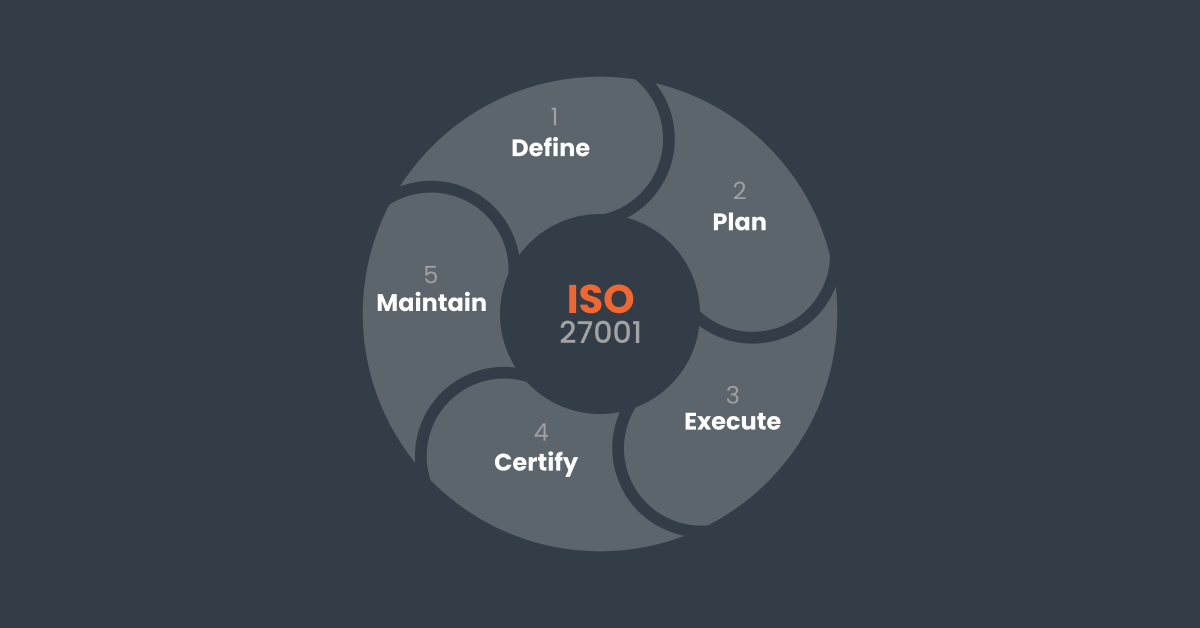
How to get your ISO 27001 certification ?
If your company is considering taking the steps to become ISO 27001 certified, here is what you can expect:
Step 1: Get everyone in the company on board
First and foremost, you will need to ensure the collaboration of the company’s management team: they must notify employees of the objectives behind the implementation of the ISMS so that all personnel are aware of the goals.
Step 2: Define the characteristics of the information security risk management regulation
In this step, the company must determine the guidelines that will allow you to estimate what risks are likely to occur in your industry. In general, this assessment should be based on the degree of danger and on security criteria.
Step 3: Risk identification and analysis
The company must analyze the risks that may threaten information security in order to establish procedures for implementing the ISMS. This is the most energy-intensive task, as you really have no room for error.
To start, it is essential to make a list of all the IT assets your company owns. If your company doesn’t have inventory management software, now is the time to get one.
Regardless of the size of your company and the number of assets it has, the standard requires you to be rigorous and accurate in the listing of your data.
Software such as Hector will be very helpful during your surveillance and recertification audits, which we’ll discuss later.
Next, you need to analyze the risks of each IT asset. You can assess these risks based on the criteria previously established in Step 2 and prioritize them according to their threat level.
Step 4: Reporting
In this step, the organization develops documents that contain the necessary measures to reduce the risks, but also documents that justify the decision on the actions to be taken, which will be useful during the certification audit.
Step 5: Testing phase
The company must test the newly integrated standard before facing a real audit in order to get its certification. This will serve to make any necessary adjustments to the risk assessments before an external audit visit.
Step 6: Certification Audit
For the final step, the organization must undergo an independent certification audit that will analyze the information security management system created by the company. If the ISMS meets the requirements, the company will obtain its ISO 27001 certification.
Step 7: Renewal of the certification
The certification must be renewed every 3 years, after a surveillance audit has been performed within the company. ISO 27001 must always be updated and adapted to environmental changes or new threats.
How can Hector help you achieve ISO 27001 certification?
With Hector, you will be able to track your IT assets so that you are ready when an audit for ISO 27001 certification is performed.
You will be able to see which assets need to be updated, repaired or completely replaced which will also save you a lot of time.
Hector also keeps track of software, so you know when licenses need to be updated and to ensure that the company is not working with potentially out-of-date or faulty software.
You can also attach a description sheet to each asset, which comes in handy when someone unfamiliar with the asset needs to use it.
You will be able to keep a record of the steps to follow for each of your assets that you have put in place to reduce risk as part of your ISO 27001 certification.
Moreover, in case of a natural disaster or major breakdown, everything will be stored in the cloud server. This will definitely save you a lot of time and costs.
Don’t wait any longer, try Hector today!
